Resource Center
-
eBook
4 benefits of SSE that explain why CISOs are adopting them to secure third-party access
Ensuring secure third-party access is a crucial responsibility of the CISO, now this is easier said than done. Explore the top 4 reasons why CISOs are preferring SSE platforms to secure their third-party access. -
Webinar
Securing Access to you Public, Private, & Hybrid Cloud Environments
With data strewn to various geographic locales, the role of security also becomes one of compliance. During this webinar, you’ll hear about our innovative solution that can help improve your security posture or achieve better data compliance outcomes even as data begins to exist in ever more locations. -
Webinar
Ransomware: Best Practices for Prevention, Mitigation, and Recovery
When things are a bit chaotic, opportunities arise for infiltrators to unleash malware as they seek cracks in your security armor.As organizations shift employees from offices to homes and back again, expect defenses to be less effective and watch for an increase in nefarious ransomware, the scourge of the internet.During this webinar, discover effective, varied, and innovative solutions to the gnarly problem of ransomware. Learn how to stop ransomware at the network and cloud boundary, pick up best practices for detecting attackers dwelling in your systems, brush up on the latest approaches to mitigate a ransomware attack, and find out best practices for recovering should ransomware strike. -
Webinar
Zero Trust Security: Making Zero Trust possible with a Security Service Edge (SSE) approach
The security winds are rapidly shifting from ‘trust but verify’ models to ones that assume that every activity is insecure until proven otherwise. In an age of high-profile security attacks, increasingly sophisticated phishing schemes, and ransomware threats run amok, organizations of all shapes and sizes are urgently seeking new ways to protect their finances, their reputations, and their business operations. As organizations strive to embrace Zero Trust methodologies as a baseline state for their security lines of defense, many continue to struggle with the best ways to achieve their goals. It can also be difficult to fully grasp the breadth and depth to which Zero Trust permeates existing processes and requires change. The potential operational impact that can result from the methodology is also intimidating. -
Webinar
Discovery Days: Streamlining, Securing, and Protecting Cloud, IT, and Business Operations
IT pros and decision makers must prioritize continuous improvement, well, continuously. The job requires constant vigilance for new opportunities to make IT environments more efficient, more secure, and better at serving the needs of the business.And it requires constant effort because the pace of innovation is furious. On-premises hardware, from blade servers to storage arrays to various appliances, is being iterated constantly. And the pace is even faster for cloud infrastructure platforms to SaaS applications, where the release cycle is measured in days, if not hours. The relative strength of one product or product category can change in weeks, as upstarts absorb functionality and upend classifications. -
Webinar
The Journey to SSE
Due to the growth of “Cloud” over the past ten years, organizations have moved from the data center to “centers of data”. As applications are now distributed, the networks and security solutions have become more complex and brittle. Adding fuel to this fire of complexity, network and security solutions must now address the demands of the hybrid workforce. In this talk, learn how you can use Security Service Edge in a simple way to solve some of the complex network security problems no matter how large your organization. -
Webinar
Modernizing Infrastructure and Cyber Security For Retail
The modern retailer is under pressure. Over the last two years, we’ve seen the rise of the seamless shopper, retailers must meet the customer in their terms and consumers are hungry for personalized experiences. Meanwhile companies, according to the Verizon’s latest data breach report, are struggling to protect not only card holder data but now personal information. -
Webinar
An Honest Conversation About Securing the Modern Workplace
In this panel session learn from industry pioneers about what’s needed to harmonize secure access for the workplace. Hear about Security Service Edge (SSE) platforms which combine ZTNA, SWG, CASB, and Digital Experience into one service, key characteristics, and use cases. There are a number of paths to choose from. There’s also a lot of hype making it difficult to figure out which approach to take. -
Webinar
Streamlining, Securing, and Protecting Cloud, IT, and Business Operations
In IT, you’re thinking about continuous improvement every day. Making your IT environment more efficient and more secure, while serving the current and anticipated needs of the organization, are constant concerns. On this event, you’ll discover innovative solutions from every corner of the IT landscape. From on-premises hardware to cloud infrastructure to software services to technologies that secure it all, everything is on the agenda for this special event. -
Webinar
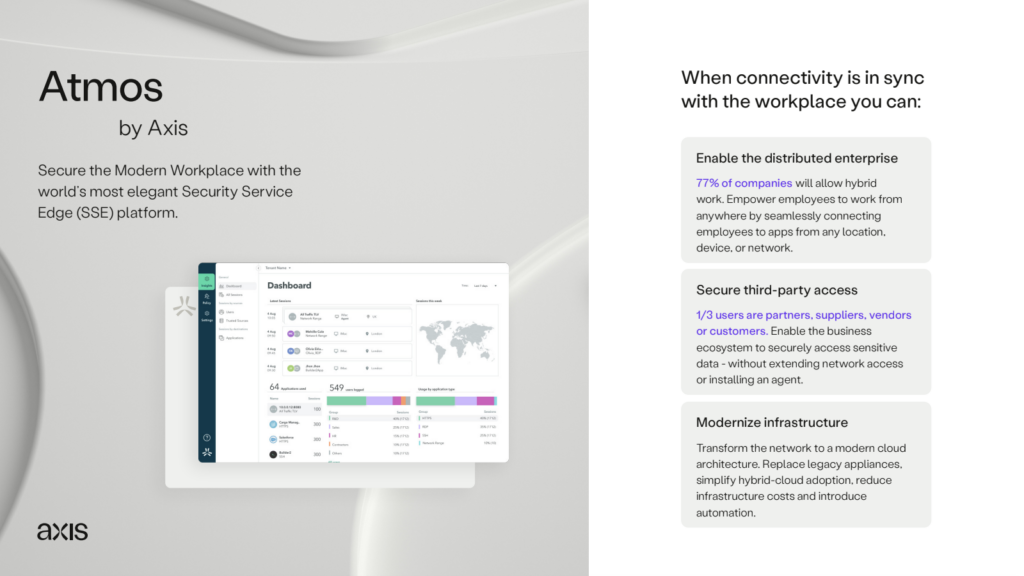
Harmonize secure access with SSE while optimizing SIEM & SOAR
The modern workplace is an orchestra composed of users, devices, applications, and clouds – each playing their own tune, and constantly syncing, and changing. This orchestra is difficult to secure, challenging to see, complex, and extends far beyond the confines of the corporate network. It requires a solution designed to harmonize workplace connectivity. In this session join a former Head of Architecture at TT Electronics, and learn how a security service edge (SSE) platform can empower IT to securely, and cost effectively, connect a modern workplace. IT can secure access to SaaS and hybrid-cloud environments, reduce their appliance footprint, adopt an “internet-connected” branch strategy, and utilize digital experience monitoring to maximize user productivity – all with a cloud-delivered service! -
Webinar
How to Use Edge Connectivity to Modernize Access to Business Data
Solutions like M365, Zoom, AWS, Azure and Jira – which offer consistent reliability, availability across hybrid work environments, and scale – are key to productivity. They’ve been widely adopted because of this. Now, the Internet is becoming the new corporate network and “network security” has become less relevant. Continuing to invest in legacy connectivity solutions like network switches, firewalls, and VPN gateways is a mismatch for the modern workplace. -
Webinar
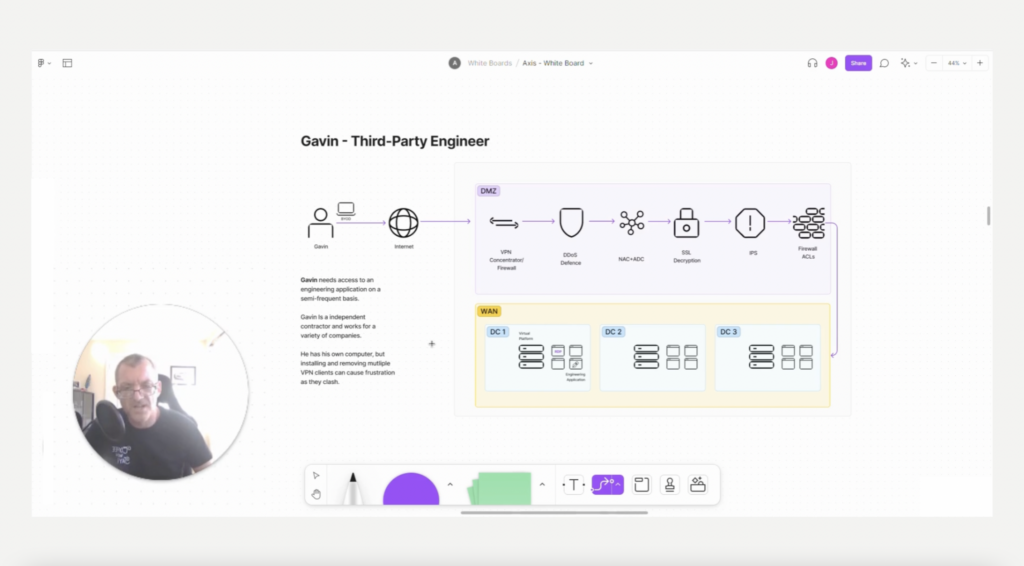
How to Power the Business Ecosystem Through Secure Access
Your business is made up of much more than just employees. There could be thousands of third-parties that interact with the business each day. These suppliers, auditors, OT vendors, and even B2B customers play a vital role in your business ecosystem. So, making it safe for partners to access your data is critical. What many IT leaders don’t know, is that with the right mindset, and secure access platform, they can make it easy to securely connect this ecosystem. They don’t have to deploy an agent on the partner’s device, nor do they need to place them on the corporate network. Instead, IT can minimize over-privileged access, and even gain valuable insights into what partners are interacting with. At Axis, they believe in a world in which workplace connectivity is always secure and seamless. Through their security services edge platform we make securing access to business resources impossibly simple. By doing so, their customers are able to make hybrid work simple, turn digital experience into a competitive advantage, and can better protect their data from cyber threats – even as it moves to cloud. -
Webinar
ISMG Cybersecurity Summit: Secure the Modern Workplace
80% of companies will allow employees to work from home or the office. We call this “hybrid work.” This has created a need for secure access services that work consistently across locations so users can work from anywhere, can scale easily without complexity, and can minimize risk of cyber threats like ransomware – by keeping users off the network. View this cybersecurity seminar On-Demand now and learn: Why ZTNA may be the first stop in your journey to zero trust and securing the edge How to enhance user productivity and ensure the best experience possible, wherever they’re working from, to avoid IT support tickets How to save time and costs by using a cloud-delivered platform to avoid expensive firewalls and MPLS -
Webinar
How Hybrid Work Killed VPN
80% of companies plan to allow employees to work from home or the office. We call this “hybrid work.” This requires a solution that works consistently across any location so that users have a seamless experience, and minimizes the risk of cyber threats like ransomware – by keeping users off the network. This is why organizations like Kayak, Copart, and Hooters are replacing remote access VPNs with zero trust network access (ZTNA). The right ZTNA service provides IT with a solution for ensuring zero trust access to business apps through identity and logical policies. With ZTNA IT can safely enable hybrid work, and integrate with other technology ecosystem investments like Okta, Azure AD and CrowdStrike that may already be in place. Join this session to learn why ZTNA may be the first stop in your journey to zero trust. -
Webinar
The Fastest Path to ZTNA and SASE: ESG’s John Grady
Most organizations want to move to zero trust network access (ZTNA) and a secure access service edge (SASE), but what strategy should you take to get there? There are a number of paths to choose from. There’s also a lot of hype making it difficult to figure out which approach to take. This webinar breaks it down for you. Join us for a discussion with John Grady from ESG Research to learn: • What organizations think they need based on input from hundreds of different IT security professionals • How to avoid the hype surrounding ZTNA and SASE solutions and implement practical solutions • Three different approaches you can take to implement ZTNA and SASE functionality -
Video
Get Rich Quick with Ransomware: A Lazy Hacker’s Perspective for Enterprises
Think Ransomware isn’t for you? In this enlightening talk, Gil Azrielant, co-founder of Axis Security, will quickly discuss the business opportunities, the technologies, the industry and the mechanics that attract hackers to ransomware. In the process Gil will reveal how some enterprises can use new technologies to defend themselves against attack.