The CASB Security Platform that’s Modernizing Access
Regulate data flows, discover Shadow IT, remain in control
Cover your SaaS
Atmos CASB allows you to easily reach the full potential of your cloud investments.
Atmos CASB
Atmos CASB allows IT to identify, manage, and control the use of cloud services. The service mediates connections between users and cloud applications, and helps discover Shadow IT to apps to ensure sensitive data in remains protected.
Weightless protection
With inline CASB for data in motion, uncover shadow IT, prevent data loss, and enforce controls
Fluent integrations
API-based CASB integrations allow automatic scanning of SaaS apps and IaaS platforms for protection

End-to-end visibility
View the entire access story with centralized management. Control what a user can access, download, and share
Embrace cloud services and applications with swagger.
Modernize access with Atmos CASB and realize value from day one
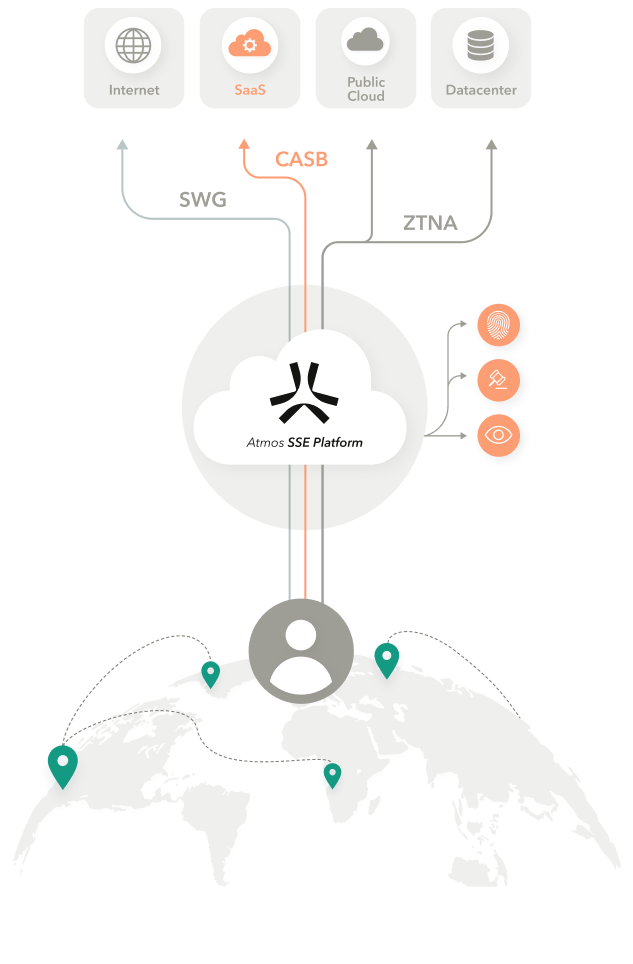
How Atmos CASB works
A user attempts to access
a cloud service
Secure access to SaaS applications and IaaS platforms
Atmos proxies traffic
Avoid passthrough connections that lead to risk – Atmos becomes the first stop
Atmos validates identity & applies policy
Apply access controls i.e. Upload, downloads, and share activities – and automatically adapt based on changes in context
Atmos securely connects to resource
Make private apps invisible to the Internet, keep users off the network, and deliver a safer connection to SaaS apps
Atmos inspects traffic &
monitors user experience
Gain visibility into user activity so you’re aware of malicious activity