The Single Vendor SASE Unicorn Halloween Costume
Halloween is here! I usually keep my costume choices a secret until the last minute. But this year, the choice is easy. A single vendor SASE Unicorn. Yeah, the “muggles” won’t get it but hey, everyone loves to party with a colorful unicorn!!!

If you are unfamiliar with single vendor SASE, here is what it is. Per Gartner, SASE is a converged network and security service which is delivered as a service. It “enables zero trust access based on the identity of the user, device or entity, combined with real-time context (such as device security posture) to enforce and govern security and compliance policies. Single-vendor SASE offerings should have a common management plane and data lake across all capabilities”. Whew. That is a lot. Let’s break that down a bit.
SASE Detailed View
The market is converging to address the “original sin” in networking. That’s a lack of security. We need to move beyond the firewall as the means of securing the data center, the branch, and the employee as new applications and employees exist in every nook and cranny of this planet. Zero trust network solutions are the path forward. SASE creates a system of adaptive trust, embeds it within the network, the endpoint, and then manages it by policy via a common framework. Simplifying this further, it’s software-defined networking with security which now covers not just the network devices but the endpoints too. Leverage identity and device posture checks via northbound APIs and presto, SASE!
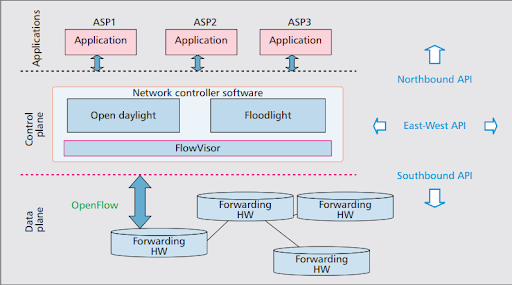
Now we’ve established the why and what, let’s get into what the landscape of solutions is currently. They currently come in two form factors. Platform and portfolio. Platform first. A fundamental rule of SASE is this, don’t impact the user experience. By this, I am referring to the number of security treatments a packet or flow will encounter on its journey from the employee to the application and back. The more treatments, the more latency. The ultimate unicorn solution will be based on a “single pass” scanning for security. Platform-based solutions with a unified network and security fabric will be able to provide this or get close to it. Unfortunately, these solutions don’t exist today. Rather, the solutions on the market today are based on portfolios. Either they started off as an SDWAN solution or as a point solution (CASB, private access, or similar). Then vendors either purchased components as part of an acquisition (most common) or combined products already in their portfolio and rebranded them to fill out their “unified SASE” portfolio. Result, non-optimal architecture with tradeoffs meaning the key rule of SASE, the user experience, is broken. Additionally, these solutions can be challenging to manage as the administration UI feels like a federation of products.
If this is the case, will the unicorn ever appear? My bet is yes and will likely come in two formats. The first form of the unicorn will be based on an SDWAN style solution. It will leverage hardware-based devices in the branch, campus …. and then wait for it… the data center. It will also incorporate the endpoint in the form of an agent for the remote worker. These points of presence will create a distributed fabric feeding back to a common management plane. Functions will be distributed but also resilient. Much like in SDWAN, if the distributed network and security fabric loses contact with the central management hub, the solution will continue to operate within a cached state. The solution will be full L7 aware and feedback to identity as well as device state repositories. The advantage is the solution can be built into common network hardware like routers, switches, and even APs. The downside is complexity. This is a lot to manage, maintain and keep synchronized.
The second SASE unicorn will be fully software-based. Rather than a distributed fabric leveraging hardware and software agents, this solution will be broker based with a distributed number of points of presence (PoP). The PoPs will reside either in the “Cloud” or take the form of a “private edge PoP” located in an enterprise data center or branch office. Resiliency is provided thru multiple PoPs in multiple Clouds (AWS, Azure, and so on) as well as the private edge. The advantages are simplification from a management solution, scalability as well as fast innovation since this solution is delivered “as a service”. The downside is you need to consider how to manage the underlay, meaning the base network to pass data back and forth.

Which unicorn will we see first? My bet is on the fully software-based solution. Hardware is hard. Software is much easier to build and innovate on. Recommendations? Right now, if someone says they have a “unified SASE solution” take it with a grain of salt. It’s likely a horse with a horn glued on it. The best advice I can give you is this. What problem are you looking to solve? If reducing the cost of your WAN and optimizing access from the branch to SaaS solutions, start with SDWAN. If your issue is enabling the hybrid workforce, look into the Security Service Edge (SSE). For this, SDWAN is not the answer. All that said, for whatever problem is your priority, make sure to ask your vendors about integrations between SDWAN and SASE. Unified SASE is not here yet, but can start to make some early steps in your journey to uncover the unicorn.