Confluenza: What is CVE-2021-26084 and why should you care
Increasingly often, the security world buzzes about a new vulnerability that keeps everyone on their toes.
A vulnerability is published on the CVE program. That means, due to the responsible disclosure procedure, that the affected vendor was already informed about it. At that point, it’s safe to assume that advanced threat actors and nation states probably already knew about it and how to exploit it effectively. However, once in the public domain, it’s a whole different ball game. Bug bounty hunters, cyber criminals, and researchers looking to make a name for themselves start the race to the effective exploit. The vendor has probably already released a patch, but patches take time to propagate, and the patch can be reverse engineered by adversaries to better direct themselves towards the vulnerable areas.
In some cases, like the notorious Conficker worm that affected virtually every windows machine online, this leads to a widespread computer worm. In others, like BlueKeep, it allows for ransomware to propagate easily and without human interaction within networks.
So what happened? (and why should enterprises be concerned)
On August 25th 2021 a remote code execution vulnerability of Atlassian Confluence was published and given the identifier CVE-2021-26084. The clever name Confluenza was later given to it. It affected virtually every version of Confluence that’s not hosted by Atlassian. A patch was made available that day, but we all know old versions die hard.
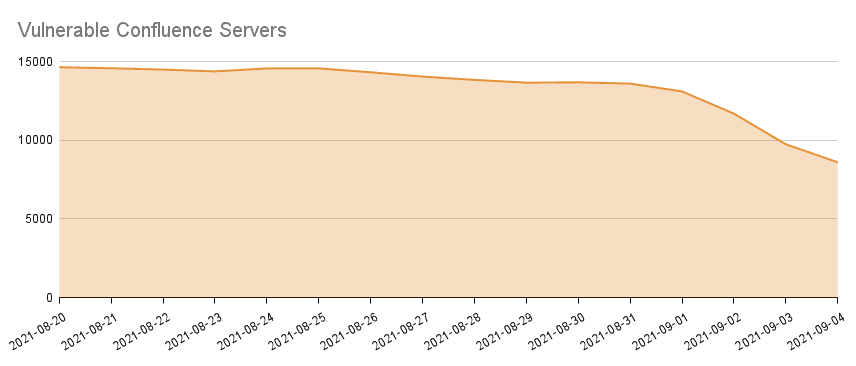
On Aug 31st, 2021, rootxharsh and iamnooob published an exploit for CVE-2021-26084. At that point, every half-savvy attacker could scan for vulnerable instances and wreak havoc.
The vulnerability took advantage of an insecure handling of OGNL, an expression language that provides syntax for evaluating expressions. Generally, it allows an attacker to craft an OGNL expression and send it to the remote server for evaluation. That evaluation can include the execution of arbitrary code on the remote server hosted on the victim’s network. Even worse in this case, the vulnerability extends to non-authenticated users so even strong auth and MFA can’t help if the threat actor has direct access to the application. Infect with ransomware? Steal data? Install a backdoor? Whatever the adversary’s goal is – this is one huge leap towards the crown jewels. This is a big deal.
Confluence is a wiki-like collaboration tool that is part of the Atlassian suite. According to Atlassian, 83% of Fortune 500 companies use their suite of products. Their products are ubiquitous among product and R&D teams. Many organizations use it as the formal means of maintaining a knowledge base, but sometimes it is introduced into the organization from the bottom upwards. Confluence is offered for a trial period for free, so teams may have set up a vulnerable instance that has since been forgotten. Think they’re going to patch it?
What’s next?
For this vulnerability, the patch is out, and it’s best to patch all Confluence servers on your network. Some WAF configurations have also been suggested, though this is not foolproof and can be circumvented, something is better than nothing.
This is not a trivial task. Organizations seldom keep a full inventory of their applications, and shadow IT is still an issue for many organizations.
ZTNA – at your service
So it would be really helpful to have all of your apps services cloaked and hidden from the public internet, and the intranet for that matter. To prevent direct access. To have every request or action accounted for. To gain out-of-the-box remediations that would have prevented this vulnerability even before it was published. That’s exactly how ZTNA is moving the legacy network security paradigm of having to be perfect every time, to a significantly reduced attack surface.
Without deploying any agents, without making modifications to the network or server, and without publishing an internet-facing endpoint – Axis already helped enterprises get full protection, visibility and control over their Confluence, Jira, and other corporate applications. When this vulnerability was released, they could remain calm. Their servers are outside the reach of scans and attackers, and the built-in sanitization and WAF capabilities would prevent even privileged users from exploiting this vulnerability.
Responding to new vulnerabilities can feel like a game of “whack-a-mole”, but organizations that adopt a Zero Trust architecture have longer time to respond, fewer possible ways in, and a much smaller blast radius when an attack does happen. There is no better time than now to make a change. Axis Security helps customers transform legacy networks to Zero Trust architecture in minutes. This is a rare opportunity to improve both security and user experience. Please don’t hesitate to reach out and let us know how Axis can help.